It seems like headlines regarding passwords, security breaches, and employee security mishaps are a daily occurrence these days:
“PIN numbers stolen in breach”
“Customers Told to Reset Passwords After Data Offered for Sale”
“Teddy bear leaks >2 million parents’ and kids’ voice messages”
“Email Not the Only Thing Breached”
“Employee Accidentally Emails 36,000 Social Security Numbers of Coworkers”
Whether it be further revelations about the scope of the Yahoo! breach, ongoing news related to state-sponsored hacking, or careless employees, information security is not a topic just for “techies” anymore. Everything we touch these days involves a password—from social media sites to bank machines—so it’s important to know if you have any password management flaws, moreover, how you can avoid them in the first place.
Given how many of our daily activities take place online—whether “serious”, like banking and accounting, or “personal”, like catching up with friends via email or Facebook—everyone needs to understand the ramifications of failing to embrace prudent password practices.
Wired reporter Matt Honan brought this topic to the mainstream in his 2012 article. He begins: “In the space of one hour, my entire digital life was destroyed.” From there, Matt details how many of his accounts for various services were compromised until it ended with hackers erasing all the data on his laptop, tablet, and phone. The article is an eye-opening read illustrating how truly connected everything is these days. And for all the upsides this brings, everyone now has a reason to take passwords and security even more seriously, given the potential consequences of access falling into the wrong hands.
This article focuses on techniques to ensure good password security, and concludes by showing how Kashoo is built to help you embrace those techniques so they become second nature, allowing you to focus on the important aspects of running your small business.
Password Management Flaws
One Password to Rule them All
This is probably the most common of all of the password management flaws out there. It’s not uncommon for people to use the same password (or a small handful of passwords) across all their online accounts. If one of those accounts is compromised it puts every other one with that same password at risk. In a world where it’s wise to assume that sites will be compromised, this means a single password provides minimal protection to all of your online assets.
While it might be convenient if your house, bike lock, gym locker, and office all used the same key, consider the risk to your physical belongings if you were to lose that key, moreover, how concerned would you be that someone might recover that key and identify that it belonged to you. And don’t discount the pain of getting all the locks re-keyed! A single password for your online accounts makes as much sense as a single key for every physical lock you require in the real world.
Memorizing
If you only had a single email account, one banking site, and a handful of utilities to log in to, then it might be feasible to memorize a half dozen passwords. But the reality is most people have tens to hundreds of sites; whether it be for shopping, reading the news, or multiple social networks, the number of accounts makes it impractical to memorize passwords. When you factor in password resets and policies to change passwords, the effort to remember strong and unique passwords across many sites truly becomes an impossible task.
Algorithms
Some people develop mental algorithms to help devise passwords. For example; one might pick a preferred food to represent every letter of the alphabet (Apricot, Beets, Chocolate, and so on). The password for a site is generated and easily reconstructed each time it is needed by keying off specific letters in the domain name (for example, the last two). In this example the password for faceboOK.com might be OliveKale.
This becomes more difficult, however, depending on the site’s password rules. If Facebook were to add a requirement for numbers then the algorithm must be modified. Perhaps the person chooses to wrap the foods inside the year their favorite baseball team (the Chicago Cubs) last won the World Series, evolving the password into 20OliveKale16. Later, when special characters become a requirement, the algorithm morphs again to inserting the character between the foods and it becomes: 20Olive#Kale16.
While it may seem clever, this approach breaks down because so many sites impose different password requirements. Varying constraints on length, both minimum and maximum, as well as limiting which characters are allowed necessitates people to remember special exceptions. If you forget a special case and are forced to reset your password to something new that you haven’t used before, you end up needing a second algorithm. Then you must remember which sites use which algorithm. What started off as a seemingly failsafe method to have mostly unique passwords devolves to be little better than memorization.
The last thing you want is for your method to remember the passwords to critical systems you access be so taxing that it distracts you from the important tasks in life.
Password Strength
Before introducing a way to maintain your sanity, let’s explore what makes a good password.
Hopefully you are not using password or 123456 as any of your passwords. But if you are, then;
- You’re not alone, and
- You’re also incredibly vulnerable
Reports from Keeper Security and SplashData estimate between 4–17% of people chose one of these as their password in 2016. Hackers know this and try these common passwords first before they resort to brute force.
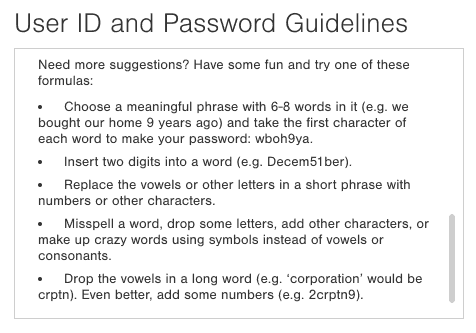
Suggestions from the Citibank UserID and Password Guidelines
Ironically, the policies of many IT departments and websites often drive users to choose short passwords that are not only hard to remember, but easy for computers to crack. While complexity and randomness are good, they make it difficult for humans, which leads people to pick shorter (and thus easier to crack) passwords.
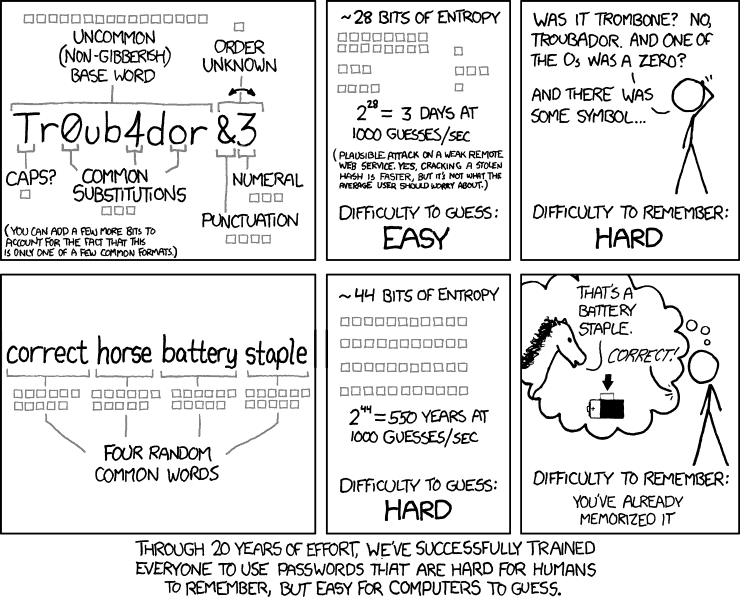
Image: xkcd, used under Creative Commons Attribution-NonCommercial 2.5 License
Increasingly, security-conscious users have been moving to passphrases—human-readable passwords composed of multiple words—as advocated in the popular xkcd web comic above. However, recent research shows that simply choosing a long alphabetic passphrase is less reliable than previously thought. With the advent of cloud computing, where hackers can rent large amounts of compute power from Amazon, Google, and Microsoft, it has become cost effective to deploy hundreds and thousands of computers at a time in order to crack passwords.
The only real option: a password manager
We know our passwords need to be longer, should include more than just letters, and be unique for every site where we have an account. How do we meet all of these goals in a sane and manageable way? The answer is in using a password management tool that helps to marshall all of a user’s credentials.
A good password manager will work for both creating and updating passwords in many contexts including websites (in browsers) and native applications. Perhaps most importantly, it must be easy to use so that it’s not tempting to bypass. Fortunately the category of password manager applications has evolved quickly, and actually makes good password habits easier and far more secure than most of the previously mentioned (and flawed) alternatives.
An effective password manager will:
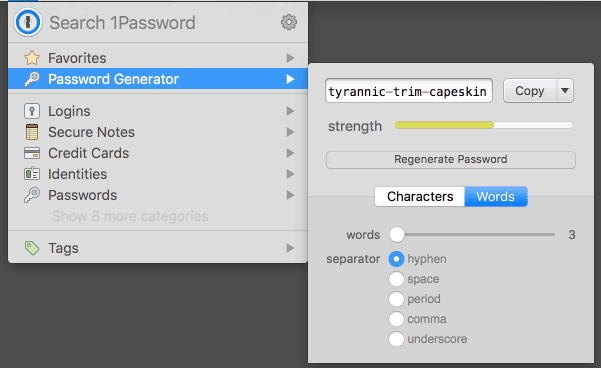
- Easily generate strong passwords unique for each website. The human brain does not effectively generate random sequences of characters or words but computers are great at it. Quickly generating new passwords and copy/pasting them into registration forms is the first critical component of an effective solution.

Generating a strong password in 1Password
- Securely store all passwords. If your computer or phone is lost or stolen, having the passwords easily visible in a file would be as insecure as writing passwords on Post-It notes and sticking it to your monitor. The password manager must encrypt the data and ensure you are the only person who can access it.
- Quickly and automatically retrieve and enter passwords. Generating strong passwords and storing them securely is useless if we can’t easily access them. Since logging into a site is the most common activity, the password manager must make this seamless. With plugins for all the popular web browsers, the leading password managers can detect which site you are visiting and securely fill in the appropriate password with a simple hotkey combo or a couple of clicks.
Other helpful features include:
- Ability to securely store notes with security questions and answers. Many sites incorporate additional challenges into the authentication process (like identifying a specific image or answering a security question), and often there are account numbers or other related information that are useful to track. Storing this data with the password is convenient and keeps it secure. This functionality means you can stop openly sharing personal information like anniversary dates, names of children and the other data which uniquely identifies you and could be used against you if it were leaked in a breach. Since you’ll be using the password manager to retrieve your password, generate a random answer like “role-shimmy-bonsai-bream” for the name of your high school and retrieve it when you retrieve the password.
- Applications for mobile devices. You probably use a smartphone or a tablet to access the internet. If the passwords are only available via the computer at your desk you’ll be less inclined to use the password manager. Avoid the temptation and choose a solution that can be with you everywhere.
- Easily syncing passwords across devices. Closely related to the previous point, once you access your passwords in multiple places you’ll need a way to keep them all in sync. Some solutions provide the option to sync between devices when they are on the same trusted network. Others offer a service component and enable synchronization via the cloud.
A few Password Manager options:
There are many options when it comes to password managers. The following products are well known and, indeed, the ones chosen most frequently by members of the Kashoo team.
- 1Password – Originally targeted for the Apple ecosystem, this product has expanded to support Android and Windows with the most recent updates targeting securely sharing passwords between members of a family or a team.
- LastPass – Easily the most comprehensive password manager on the market with support for Linux, Chromebooks, and Opera, as well as other more mainstream platforms. Notably this product took top honors in The Wirecutter’s in-depth review of password managers.
- Pass – For readers with a technical background insisting on an open source solution, this project has gained momentum as other projects have faltered. Setup is not trivial but the community is very active and has written plugins and applications allowing it to compete with the previous two solutions, once configured.
Kashoo makes it easy to focus on your business, not passwords
If you’re not yet convinced to use a password manager, consider using the Google or Facebook login options to sign in. First, set a very strong password on your Kashoo account, which could later be recovered through the “Forgot your password?” flow on the Kashoo login screen. Next, link your Kashoo account to Google or Facebook. You won’t have to remember a password for Kashoo and you’ll have the considerable resources of Google and Facebook working to protect that account. The technology that makes it all work is OAuth2, an industry standard which has undergone peer review by security experts.
Need to share the details of your business finances with a business partner or your accountant? DO NOT SHARE YOUR PASSWORD! Instead, invite additional people to your business at no extra charge. They will have their own account secured with their own unique password. Better yet, refer them to this post to make sure they are following best practices when it comes to passwords.
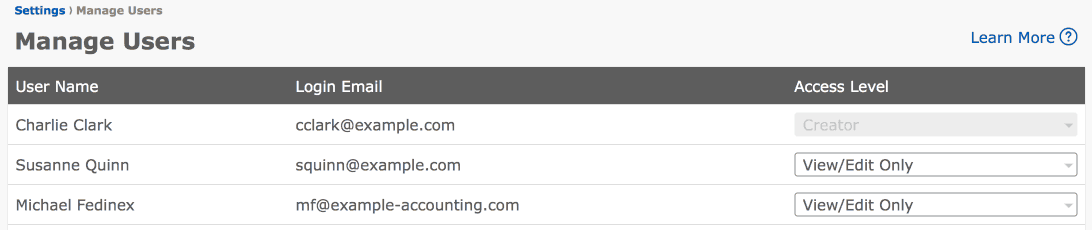 Configuring multiple users with access to a business in Kashoo
Configuring multiple users with access to a business in Kashoo
In the Kashoo iOS app we have integrated the 1Password extension from AgileBits, which enables easy access to third-party password management apps from within Kashoo and avoids the need to type or copy and paste anything.
Finally, if you’re using an iOS device with Touch ID capabilities, you can protect access to the Kashoo app by requiring your fingerprint. For older iOS devices, a requiring a PIN code to unlock is an alternative.
Conclusion
There is a lot to consider when it comes to data security, but avoiding the aforementioned password management flaws and beefing up password practices is an easy thing that everyone can do. Using a password manager can improve your online life, making it both better protected and more convenient, too.
Additional Resources
Are you curious if your account may have been compromised? Check out the site Have I been pwned to see if you may have been impacted by known breaches at large sites like LinkedIn, Dropbox, Adobe, Comcast, and Snapchat, in addition to many smaller and regional sites.
Want to know how long it would take a computer to crack one of your passwords? Check out passfault.com from OWASP, a well respected organization with the mandate to “drive visibility and evolution in the safety and security of the world’s software.” Passwords with a minimum length of 8 characters have long been the standard but passwords containing 8 letters can now be expected to be cracked in a matter of hours.